I’ll admit to not having accomplished a radical verification. Nevertheless, I’d nonetheless wager cash that AAA/RBAC companies are extra continuously talked about on Cisco certification blueprints than some other networking subject. From the CCNA to the Knowledgeable stage, you’ll discover AAA, TACACS+, RADIUS, and RBAC listed on the examination subjects.
Here’s a handful of examples should you’d prefer to test it out your self:
- 200-301 CCNA
- 2.8 Describe AP and WLC administration entry connections (Telnet, SSH, HTTP, HTTPS, console, and TACACS+/RADIUS)
- 5.8 Differentiate authentication, authorization, and accounting ideas
- 350-401 ENCOR
- 5.1 Configure and confirm gadget entry management
- 300-410 ENARSI
- 3.1 Troubleshoot gadget safety utilizing IOS AAA (TACACS+, RADIUS, native database)
- 300-430 ENWLSI
- 8.1 Implement gadget entry controls (together with RADIUS and TACACS+)
- 350-701 SCOR
- 2.7 Configure AAA for gadget and community entry reminiscent of TACACS+ and RADIUS
- 300-715 SISE
- 7.0 Community Entry Gadget Administration
- 350-601 DCCOR
- 5.xa Apply community|compute|storage safety – AAA and RBAC
- 300-615 DCIT
- 5.xb Troubleshooting community|compute|storage safety – AAA and RBAC
- 350-501 SPCOR
- 1.6b Describe administration airplane safety – AAA and TACACS
- 300-540 SPCNI
- 4.1e Implement infrastructure safety – TACACS
OMG. That’s 10 completely different certifications from Affiliate to Skilled the place these subjects present up. You’ll additionally discover them on Knowledgeable-level exams, such because the Enterprise Infrastructure, Enterprise Wi-fi, Safety, Service Supplier, and Knowledge Heart labs. (If anybody on the market can discover one other subject with as broad a protection, please let me know within the feedback. I’d like to know what I’ve neglected up to now.)
Go to the Cisco Studying Community to view the examination subjects for all Cisco certification exams. View examination subjects
Okay… it’s positively vital… however what is AAA?
AAA is a vital subject, but it surely’s one which even long-time community engineers could not totally perceive. So earlier than we see it in motion, how a few fast overview of what the “triple A’s” imply?
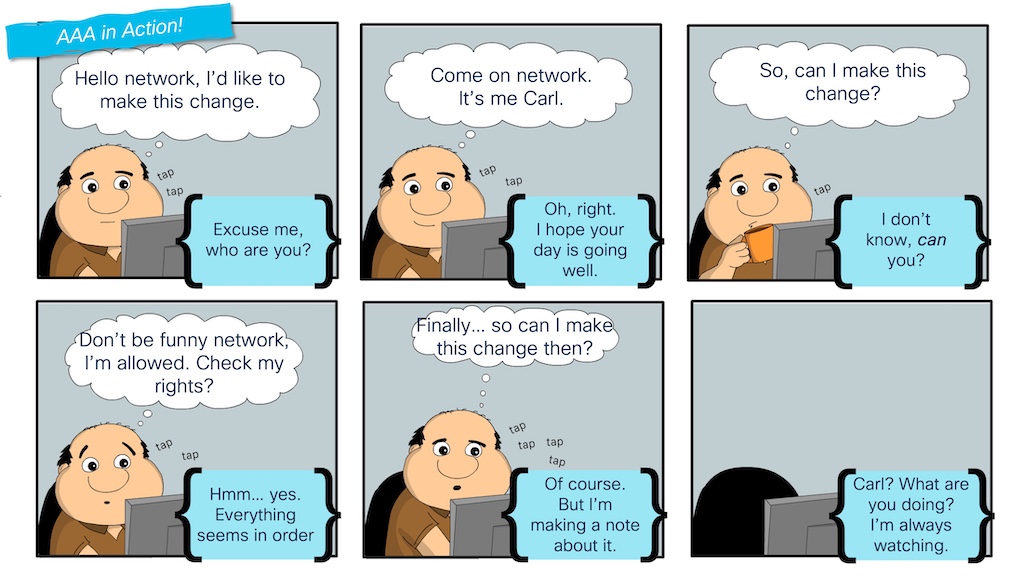
Within the “AAA in Motion!” comedian, Carl experiences your entire AAA course of:
- The primary “A” stands for Authentication. We see this represented when Carl is prompted to confirm his identification earlier than he’s allowed to make a change to the community.
- The second “A” stands for Authorization. Even after the community verifies Carl’s identification, he has to test whether or not he has the best(s) to make this alteration, primarily based on which rights he has been granted on the community.
- And the third and last “A” stands for Accounting, which Carl sees in motion when the community logs the change he makes to the community.
TACACS comes into the image to assist the centralized administration of customers, roles, and logs (authentication, authorization, and accounting). Whereas every community gadget may very well be regionally configured to deal with AAA, this doesn’t scale nicely for enterprises. A greater answer is for every community gadget to speak with a central “server” for these actions. TACACS is a protocol that community gadgets and servers use to speak and deal with every of the “A’s.” A “TACACS Server” is a software program software that helps the TACACS protocol.
Can we get to the Exploration, already?!
Now that we perceive the vital position that AAA performs in a community (and that it’s a necessary subject throughout many certifications), I’d like to indicate you methods to examine and put together for it utilizing my favourite community simulation/virtualization device: Cisco Modeling Labs (CML). As a result of I’m all about sharing my exploration actions, I posted a few CML topology information on GitHub within the CML-community repository beneath Cisco DevNet.
You’ll see that one CML topology consists of simply an IOL router, whereas one other provides a Nexus 9000v swap to cowl knowledge middle platforms as nicely. So, after you’ve learn this weblog put up, positively obtain the topologies and discover them your self.

The right way to run a TACACS Server in Cisco Modeling Labs
Earlier than you possibly can configure TACACS on a swap or router, you will need to have a TACACS server accessible within the community. A standard TACACS server for a manufacturing community is Cisco ISE, a full “identification companies engine” for gadget administration, community entry, wi-fi safety, VPN entry, and extra.
Cisco ISE is a vital product and subject for community engineers. The truth is, we’ve got a certification examination devoted to it. And when you can add Cisco ISE to a CML node library utilizing the node definition accessible on the CML-Group, working a full ISE server within the topology can really feel overkill when the main target is simply on configuring TACACS for gadget administration.
Fortunately, there are light-weight options. My go-to possibility is the open-source “tac_plus” software that has been accessible for a few years. Tac_plus is a primary Linux software that may be downloaded and put in on most Linux distributions. Whereas lively growth of the challenge appears to have stalled, it really works nice and continues to be a superb possibility for instances reminiscent of this.
Should you have a look at the picture of the CML topology, you’ll see “aaa-server” on the left-hand facet of the diagram. It is a customary Ubuntu node from the CML reference platforms, with a beginning configuration setup to put in tac_plus and configure it as a primary TACACS server. Be happy to go and take a look at the configuration within the topology file for full particulars, however listed here are the fundamentals of what I did to construct my TACACS server:
- Set up the necessities to obtain and set up the tac_plus software from supply code.
- Create the “tac_plus.conf” configuration file to specify the TACACS secret key, customers, and roles/privilege ranges for each IOS and NX-OS platforms.
- Create a “tac_plus.service” file to setup tac_plus as a service.
- Obtain, extract, set up, and begin the tac_plus server.
With the set up and configuration of the aaa-server a part of the bottom CML topology file, tac_plus will probably be working and able to take requests as quickly because the lab is began.
cisco@aaa-server:~$ systemctl standing tac_plus
● tac_plus.service - tac_plus Service
Loaded: loaded (/and so on/systemd/system/tac_plus.service; enabled; vendor pres>
Lively: lively (working) since Mon 2024-10-14 19:16:37 UTC; 2s in the past
Major PID: 5982 (tac_plus)
Duties: 1 (restrict: 2310)
Reminiscence: 416.0K
CPU: 2ms
CGroup: /system.slice/tac_plus.service
└─5982 /tacacs/sbin/tac_plus -G -C /and so on/tacacs/tac_plus.conf -d 8 >
Oct 14 19:16:37 aaa-server systemd[1]: Began tac_plus Service.
Oct 14 19:16:37 aaa-server tac_plus[5982]: Studying config
Oct 14 19:16:37 aaa-server tac_plus[5982]: Model F4.0.4.28 Initialized 1
Oct 14 19:16:37 aaa-server tac_plus[5982]: tac_plus server F4.0.4.28 beginning
Oct 14 19:16:37 aaa-server tac_plus[5982]: socket FD 4 AF 2
Oct 14 19:16:37 aaa-server tac_plus[5982]: socket FD 5 AF 10
Oct 14 19:16:37 aaa-server tac_plus[5982]: uid=0 euid=0 gid=0 egid=0 s=11063704>
The right way to allow AAA and TACACS on a Cisco IOS Router
With our TACACS server up and operational, we are able to now configure our IOS router to make use of it. Earlier than configuring the TACACS server on IOS, we have to guarantee some primary “pre-work” is completed on our router. IOS has been round for years and has skilled many modifications in how authentication and authorization are dealt with.
So, the very first thing we need to do is make sure the “new mannequin” of AAA is enabled on our gadget:
aaa new-model
Subsequent, we need to create a neighborhood person account that may entry and administer the gadget if the TACACS server turns into unreachable. You may also need to use a neighborhood account for serial/console connections.
username cisco privilege 15 secret cisco
On this command, the username and password are each set to “cisco.” (Not probably the most safe alternative, however that is only a lab.) The “privilege 15” a part of the command signifies that this person will probably be assigned an “administrator” position. Privilege 15 is the very best stage on an IOS gadget and permits the person to execute any and all instructions.
We’re able to configure and take a look at TACACS now. However first, I leap onto the console for the server and begin monitoring the logs. This fashion, I can test and confirm outcomes on the server facet in addition to on the consumer.
# On aaa-server journalctl -fu tac_plus # Output Oct 14 19:16:37 aaa-server systemd[1]: Began tac_plus Service. Oct 14 19:16:37 aaa-server tac_plus[5982]: Studying config Oct 14 19:16:37 aaa-server tac_plus[5982]: Model F4.0.4.28 Initialized 1 Oct 14 19:16:37 aaa-server tac_plus[5982]: tac_plus server F4.0.4.28 beginning Oct 14 19:16:37 aaa-server tac_plus[5982]: socket FD 4 AF 2 Oct 14 19:16:37 aaa-server tac_plus[5982]: socket FD 5 AF 10 Oct 14 19:16:37 aaa-server tac_plus[5982]: uid=0 euid=0 gid=0 egid=0 s=1106370448
Within the above command, the “-f” argument “follows” the log messages as they arrive in. And the “-u tac_plus” possibility limits the output to solely message from the tac_plus service.
Wonderful. Now, again to the router to configure the tacacs server and add it to a bunch of servers that the router can use for AAA service.
tacacs server aaa-server deal with ipv4 192.168.0.10 key tacacs123 aaa group server tacacs+ AAA-TACACS server title aaa-server
I’m at all times a fan of testing that one thing will (or doubtless will) work earlier than continuing. Conveniently, IOS helps a “take a look at aaa” command that we are able to use.
take a look at aaa group AAA-TACACS iosadmin admin123 legacy # Output Making an attempt authentication take a look at to server-group AAA-TACACS utilizing tacacs+ Consumer was efficiently authenticated.
That appears nice! And I can see the logs on “aaa-server” as nicely.
Oct 14 19:55:16 aaa-server tac_plus[6473]: join from 192.168.0.1 [192.168.0.1] Oct 14 19:55:17 aaa-server tac_plus[6473]: login question for 'iosadmin' port unknown-port from 192.168.0.1 accepted
With a robust sense of confidence, let’s full the AAA configuration for all three “A’s.”
! Authentication aaa authentication login default group AAA-TACACS native ! Authorization aaa authorization exec default group AAA-TACACS native aaa authorization console ! Accounting aaa accounting exec default start-stop group AAA-TACACS aaa accounting instructions 1 default start-stop group AAA-TACACS aaa accounting instructions 15 default start-stop group AAA-TACACS
Sustaining that robust sense of confidence, let’s see if it really works. Finish/exit on the router till that you must log again in.
ios01 con0 is now accessible Press RETURN to get began. Consumer Entry Verification Username:
Attempt to log into the router utilizing the TACACS credentials for the IOS gadget.
Consumer Entry Verification Username: iosadmin Password: ios01#
Success! Test the logs on the server, and you need to see one thing like this:
Oct 14 20:05:03 aaa-server tac_plus[6492]: login question for 'iosadmin' port tty0 from 192.168.0.1 accepted Oct 14 20:05:03 aaa-server tac_plus[6493]: join from 192.168.0.1 [192.168.0.1] Oct 14 20:05:03 aaa-server tac_plus[6493]: Begin authorization request Oct 14 20:05:03 aaa-server tac_plus[6493]: do_author: person="iosadmin" Oct 14 20:05:03 aaa-server tac_plus[6493]: person 'iosadmin' discovered Oct 14 20:05:03 aaa-server tac_plus[6493]: exec authorization request for iosadmin Oct 14 20:05:03 aaa-server tac_plus[6493]: exec is explicitly permitted by line 6 Oct 14 20:05:03 aaa-server tac_plus[6493]: nas:service=shell (handed through) Oct 14 20:05:03 aaa-server tac_plus[6493]: nas:cmd* (handed through) Oct 14 20:05:03 aaa-server tac_plus[6493]: nas:absent, server:priv-lvl=15 -> add priv-lvl=15 (okay) Oct 14 20:05:03 aaa-server tac_plus[6493]: added 1 args Oct 14 20:05:03 aaa-server tac_plus[6493]: out_args[0] = service=shell enter copy discarded Oct 14 20:05:03 aaa-server tac_plus[6493]: out_args[1] = cmd* enter copy discarded Oct 14 20:05:03 aaa-server tac_plus[6493]: out_args[2] = priv-lvl=15 compacted to out_args[0] Oct 14 20:05:03 aaa-server tac_plus[6493]: 1 output args Oct 14 20:05:03 aaa-server tac_plus[6493]: authorization question for 'iosadmin' tty0 from 192.168.0.1 accepted Oct 14 20:05:03 aaa-server tac_plus[6494]: join from 192.168.0.1 [192.168.0.1]
I’ve coloured the server output to focus on the authentication and authorization logs individually, displaying that they honestly are two completely different phases.
However what concerning the last “A” for accounting? Press Cntr-C to cease following the service log and open up the “accounting log.”
tail -f /var/log/tac_plus.acct # Output Oct 14 20:05:03 192.168.0.1 iosadmin tty0 async begin task_id=12 timezone=UTC service=shell
You must see a message just like the above displaying the “begin” of the session on the router. Return to the router and run “write mem” to avoid wasting the configuration modifications to reminiscence. A brand new log message ought to present up within the accounting log:
Oct 14 20:10:11 192.168.0.1 iosadmin tty0 async cease task_id=13 timezone=UTC service=shell priv-lvl=15 cmd=write reminiscence
And now, exit the router to sign off. A brand new message ought to seem as nicely:
Oct 14 20:11:02 192.168.0.1 iosadmin tty0 async cease task_id=13 timezone=UTC service=shell disc-cause=1 disc-cause-ext=9 pre-session-time=6 elapsed_time=89 stop_time=1728936662
And BAM. All three “A’s” have been validated. Wonderful work!
Hopefully, this weblog has gotten you excited to finish your individual exploration of AAA and TACACS. And, you might be in luck—the CML topology information that I discussed above (and can once more under) are there so that you can seize and use instantly. Inside them are lab guides that stroll by way of another vital AAA subjects, reminiscent of utilizing native accounts on the console/serial line for IOS and configuring TACACS on Nexus gadgets. Nevertheless, I encourage you to do some unbiased exploration and experiment with issues which might be not within the information:
What occurs should you sort the unsuitable username/password? What occurs if the configured “tacacs key” is unsuitable? What occurs if the TACACS server is unreachable?
Understanding the influence of issues and failures is vital to a community engineer’s means to be snug when one thing goes unsuitable in “actual life.” It’s a lot better to interrupt issues within the lab than watch for manufacturing to have points. And there’s no higher device than Cisco Modeling Labs for that exploration.
My very own AAA exploration will proceed. On this weblog and lab, I solely scratched the floor of the subject and information wanted for various certifications. RADIUS servers can be utilized as a substitute of TACACS, and what about AAA for issues like VPN authentication, community entry with 802.1x, or different platforms like ASA firewalls?
There are such a lot of extra potentialities for me to discover in later weblog posts. Would you prefer to see extra on AAA from me? Let me know within the feedback.
Till subsequent time!
Sources
Join Cisco U. | Be a part of the Cisco Studying Community.
Observe Cisco Studying & Certifications
X | Threads | Fb | LinkedIn | Instagram | YouTube
Use #CiscoU and #CiscoCert to hitch the dialog.
Share:

